Whether you're new to the world of document security and rights management, or you've been following developments in this specialized sector for years, the ever-changing landscape of digital publishing and secure document sharing can make choosing and implementing a solution overwhelming.
As one of the first DRM software developers to emerge in the late 1990s, we've worked closely with hundreds of organizations as they experiment with ways to balance their requirement for controlled access to documents with the need to provide as seamless an end-user experience as possible.
Our conversations with customers normally begin with the big questions of DRM architecture--e.g., Is it better to enforce security via a plug-in or simply in the web browser? Is it possible to integrate document permissions with corporate user identities? What is the best way to authenticate end-users?
But often, the need for a particular feature is foremost on their minds. These "advanced" use cases come from the ways in which organizations use digital documents in the real world. For example-- a multinational bank needs to distribute digital cashier checks such that they can only be printed on a single device at their secure location. Or, a sales department wants a document to expire after 20 minutes.
If we can add one of these "advanced" features to our technical framework, our policy has always been to build it and roll it into our offering to all our customers. The cumulative effect of incorporating these new functionalities is a rich set of tools for all our licensees to pick and choose from as their use-cases dictate.
We've recently updated our DRM Feature Checklist to include these "advanced" features along with our standard functionality. If you're currently researching possible DRM solutions, we invite you to use this checklist to compare offerings. If you're already a FileOpen customer, perhaps you'll discover a feature you didn't realize was there.
Since it's a long list, we've broken up the DRM Feature Checklist into categories: Security, Permission Options, Printing & Watermark Options, Authentication Options, End-User Experience, Admin Tools, Customization Options, Enterprise/Developer Extensibility, and Data Gathering/Analytics.
You can also get it as a PDF here: The Ultimate DRM Feature Checklist.
Security
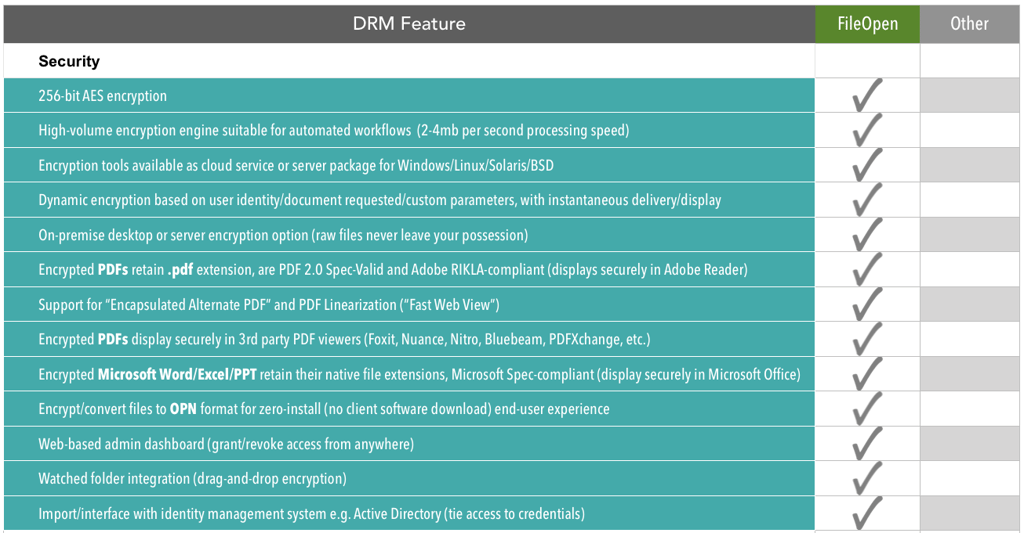
Good DRM begins with strong encryption. AES 256-bit encryption is the industry standard for government and enterprise-grade security. But encryption key length should be just the beginning of a DRM security discussion. Some important follow-up questions to ask:
- Where are the documents being encrypted? What happens to the raw unencrypted files? (desktop? on-premise server? the cloud?)
- Do files have to be encrypted in advance or can they encrypt "on-the-fly" based on dynamic data?
- What is the resulting file format of the encryption? Is it still a .pdf or .xlsx? Can it be viewed by authorized users in the standard viewing applications for those file formats?
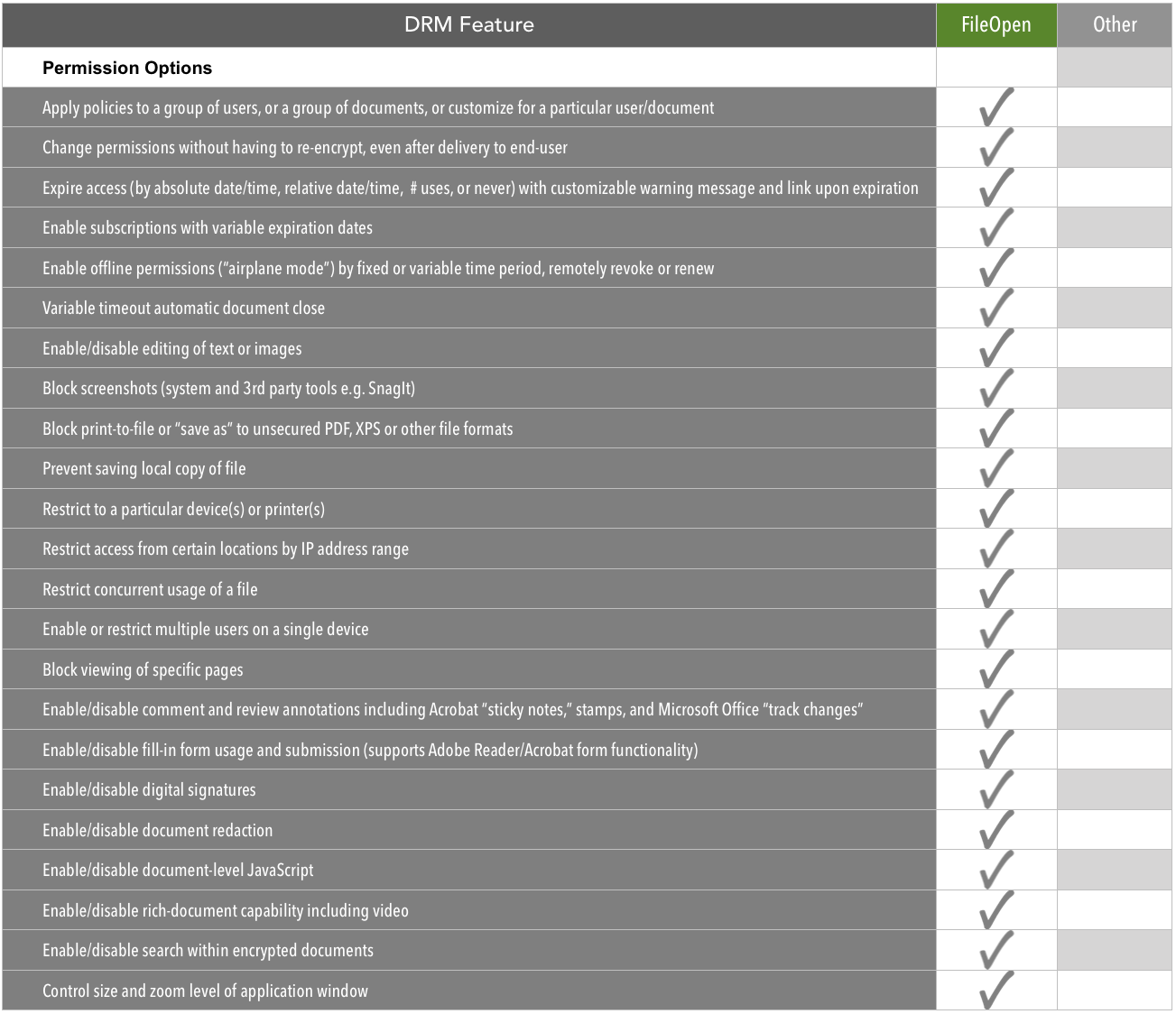
Permission Options
So you've granted someone access to your encrypted document--now what are you going to let them do with it? This is the area where many of our "advanced" DRM features appear. Some features, such as the expiration options, enable paid subscription models for publishers, or version control in corporate settings. Others maintain the usability of documents, such as supporting "track changes" mode in Word documents, while remaining encrypted.
Again, you'll want to ask where and how these permissions operate.
- Is the "key" to open the document located in the file itself or in metadata outside the file?
- Do the access controls such as expiration work in all viewing applications (Adobe Reader and other PDF viewers, MS Office viewers) or just one?
- Can you change a user's permissions after they've downloaded the file?
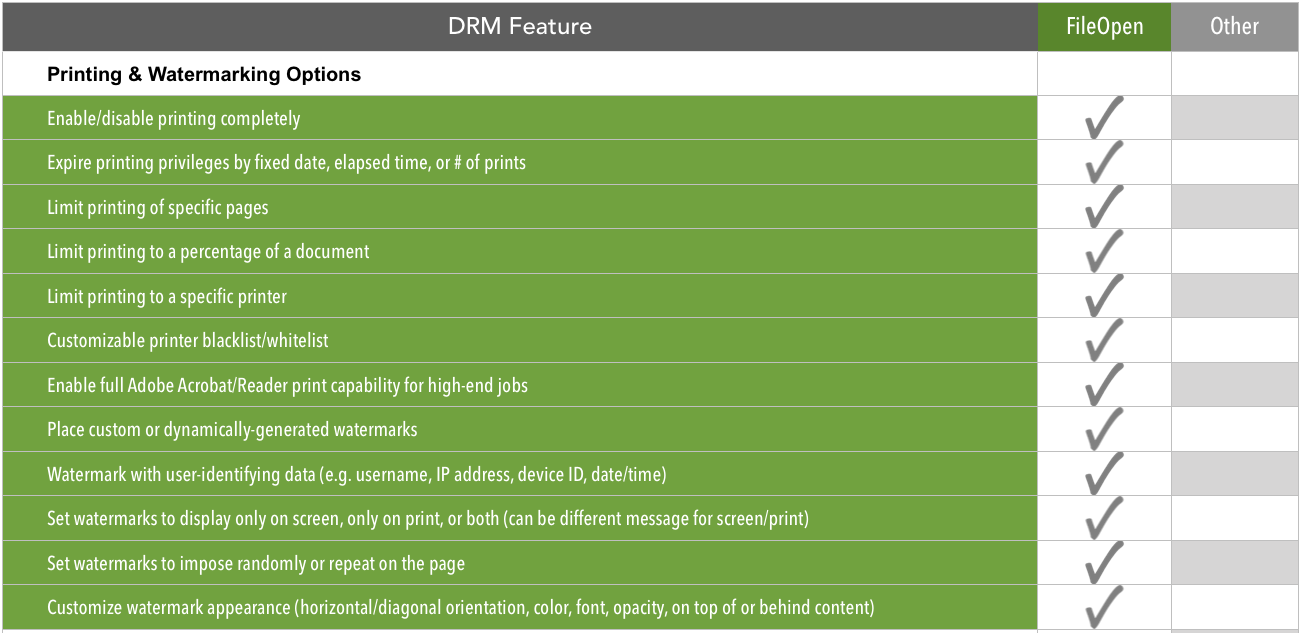
Printing & Watermarking Options
Most basic password security methods let you prevent printing. However by controlling printing through DRM, you can do some interesting things and gather valuable data about how your documents are being used. For example, you can log every print job that a particular user initiates for each document. You can also create a watermark that only appears on the printed version, which contains dynamically-generated data about the user, location, date/time, device, or other custom parameters. Conversely you can impose a watermark on the screen version only, which does not appear on the printed version (perhaps after a payment event).
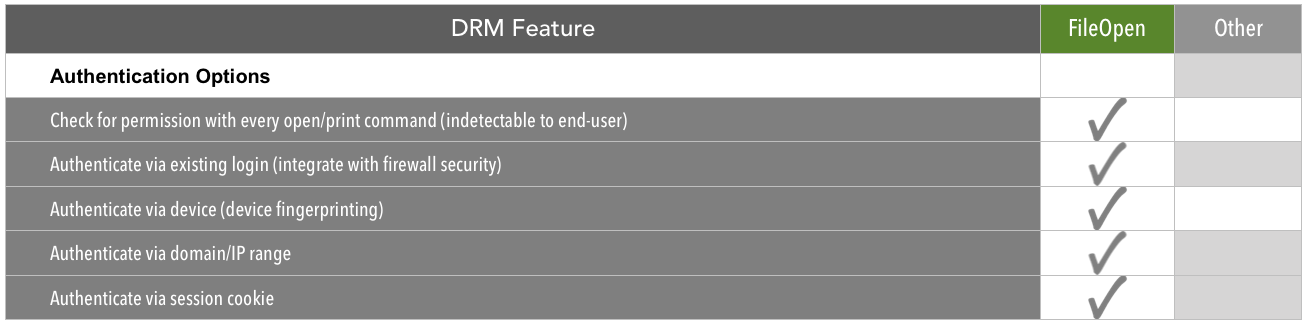
Authentication Options
How will you determine whether a user is authorized to view your encrypted documents? The more options you have here, the more flexibility you'll have in giving your authorized users a smooth viewing experience. For example, you can set your permissions to allow seamless viewing of an encrypted file when a corporate user is logged into their VPN. Their existing login credentials extend to the file permissions, so they don't need to enter a password.
You can also set your permissions to authenticate via one or more device IDs. After a user has registered a device such as their smartphone, they can view encrypted files with no password entry, while the security persists. You can grant access to a particular device, or to a # of devices per user up to the limit of your choosing.
What about offline viewing, in "airplane mode" or cellular dead zones? As an admin you can grant a user offline viewing privileges for a period of time, and their device will check in to renew the authentication automatically when the user regains internet connectivity.
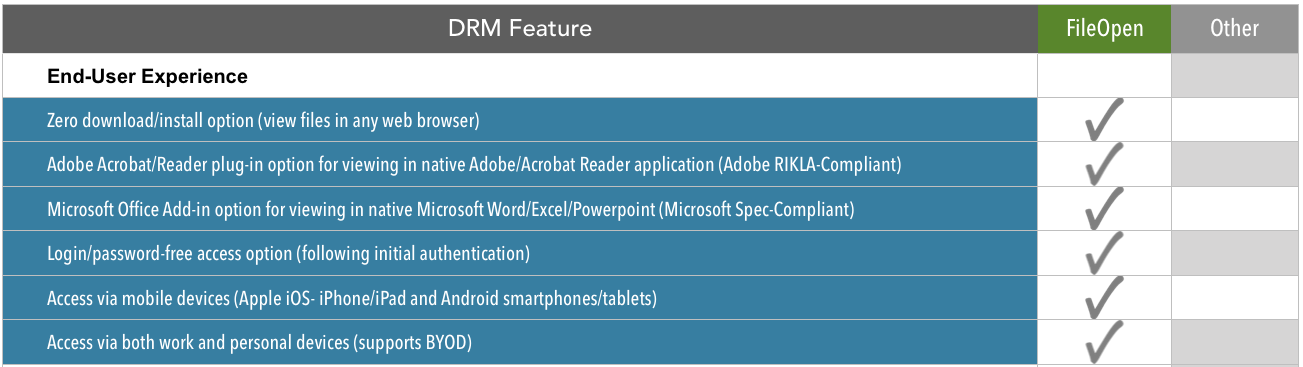
End-User Experience
DRM as a technology is still shaking off the bad rap it got in the early days of clunky DRM products. It wasn't so much that would-be pirates and leakers objected on ideological grounds, but that forcing paying customers to download special software to "unlock" encrypted files produced a lousy end-user experience.
Today, with exponentially faster Internet speeds, connected mobile devices, and more sophisticated authentication mechanisms, end-users often are not aware that they are accessing encrypted content.
Rather than decide for our customers the right balance of security, access controls and end-user ease-of-use, we provide a set of options so that you can decide where you want to land on the security - usability spectrum. Are you in a corporate setting where security is paramount and installing a small plug-in to Adobe Acrobat or Microsoft Office across the organization is no big deal? Or are you selling an e-book to millennials who want to read it instantly on their tablet? Whatever your use case, you'll want to envision your end-user experience before all other considerations, and put yourself in their shoes by testing it out from start to finish.
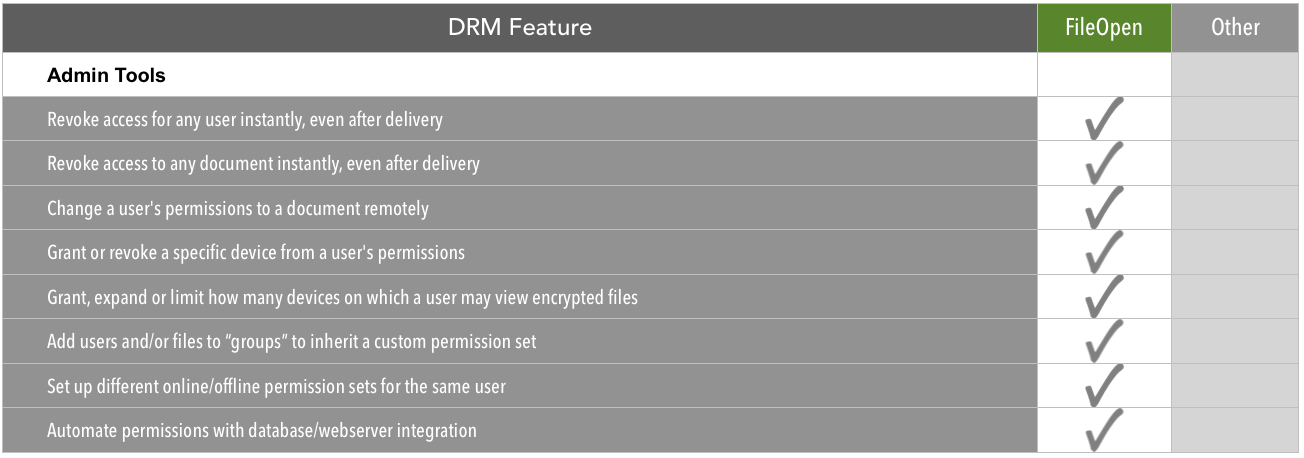
Admin Tools
Once you've encrypted your files, your admin dashboard is where you'll set up user permissions and policies and maintain them going forward. Your DRM admin controls are what differentiate rights management solutions from plain old password security. When you send out a file with password security, the process is over--the file is out there, and anyone with the password (or a good guess, or a crack) can open it. With a robust DRM solution such as RightsManager or RightsServer, you have the power to change someone's access permissions or revoke them entirely, even after they've downloaded it. You can also reset an expiration date, expand permissions, grant additional devices, and enable offline viewing for a defined period.
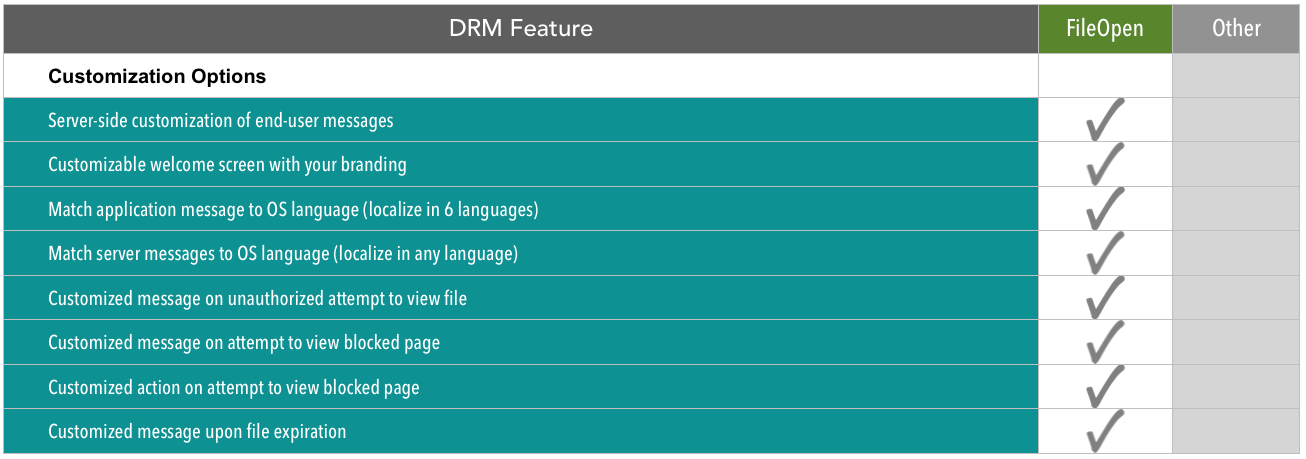
Customization Options
When you are distributing documents to an international user base, or in a specific country, it helps to display system messages in their native language. Our customization tools allow you to localize and customize alerts for document expiration, unauthorized access, etc. simply by matching the messaging to the OS settings of the user. So if a user purchases one of your documents in France, the FileOpen software will automatically detect the preferred language of the user and display messages in French. Our customization tools can also be used to include your logo, color scheme, and other branding into user interactions.
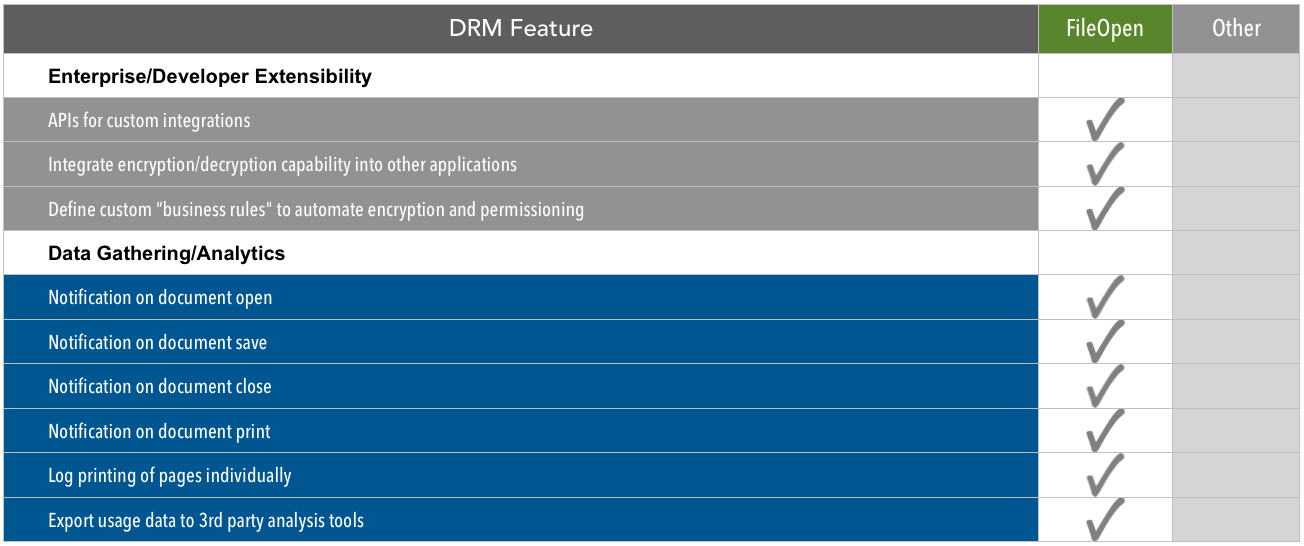
Enterprise/Developer Extensibility and Data Gathering
Chances are, you are not deploying DRM in a vacuum. You have document production workflows, databases of users, a corporate firewall or perhaps an ecommerce portal. The more you can integrate your DRM solution into these existing systems, the less work it will be to set up DRM and maintain it going forward. A silo'd DRM solution is unlikely to last long if the data inside it can't be synced with the rest of your organization.
We offer an open API for tight integration with databases and complementary security infrastructure. Developers can also modify our PermissionServer logic according to the business rules of their organization, enabling high-volume, automated encryption and authentication.
Because FileOpen's authentication technology can check and log every open/print command, there is a wealth of data you can gather and analyze about usage of your encrypted documents. When, where, and how each user is using each document can be aggregated to tell a powerful story about the reach of your information.
If you'd like to learn more
You can get the full, printable Ultimate DRM Feature Checklist here, and feel free to contact us with any questions.
For more background on DRM, and tips on how to make the most of rights management in your organization, check out our free ebook, "The Thinking Person's Guide to Document Rights Management."