The more things change, the more they stay the same
In the early 1990’s client server architectures were ubiquitous. Businesses managed their own servers, software, and productivity tools for their workforce. In the 2000’s, the growing adoption of the Web introduced new opportunities and serious new threats to the IT landscape. Businesses responded by installing more infrastructure; typically more hardware in the data center. The idea was to establish a perimeter around the business to keep hackers out and intellectual property (IP) in. Fast forward to 2010, the world had completely changed: Web access was ubiquitous. Social media, collaboration tools, file sync-and-share, and mobility (BYOD) were unstoppable forces. However, the more things changed the more the need to protect sensitive, regulated or corporate IP stayed the same.
Today businesses have embraced this new era, accepting easy-to-use, always-available productivity tools delivered to everyone in their workforce, anywhere in the world, on all their devices, in real time. By doing so, these companies not only realize a broad array of capabilities but a distinct cost savings of no longer maintaining servers and software in-house. However, the downside is that centralized, perimeter-based security solutions no longer make sense.
So, the question becomes: do you trust security measures provided by third party Web-based service providers, or do you apply client-side security to persistently protect your IP?
Client-side vs. Web-based document encryption
With Web-based encryption, documents are encrypted by the sender, at the server, so that only the receiving party can decrypt them. This approach is designed to keep files safe during transfer, but both ends are often left vulnerable. For example, in October 2014, Dropbox was a victim of a sender side breach. Dropbox users had their usernames and passwords released on Reddit, giving millions of Internet users access to the contents of their accounts. Because the content stored in the cloud was not encrypted, any user with credentials could access that content.
Had those same documents been encrypted prior to being uploaded to Dropbox, the damage would have been significantly reduced. With client-side encryption your documents are always protected; only authorized users can access the content no matter how the document is obtained or where it is stored. The same goes for your third-party service providers, with client-side encryption your Web App providers have “zero knowledge” of your content; meaning they can’t access or disclose your company’s private information. Client-side encryption is the only option that offers that kind of security.
In addition to security, client-side tools have definite business benefits. With client-side encryption tools your workforce is equipped to apply document encryption on the machine they use to author high-value documents. It is always available; empowering your workforce to easily apply document security measures without opening a browser, remembering credentials, or additional steps. Furthermore, having the encryption App local to the machine increases the likelihood of it becoming part of the user’s daily routine; a constant IP protection reminder, if you will.
FileOpen Solutions
At FileOpen, we have been building document security solutions for our customers since the early 90’s. We were the first Adobe Technology Partner to build a third party plug-in to control access and usage of PDF documents. The solution consists of three basic components; document encryption tools, a permissioning server to govern access and usage, and a versatile set of clients and viewers. Customers have the option to host their own permissioning server, RightsServer, or leverage a hosted version, RightsManager. Both solutions offer true client-side document encryption tools. Put simply, we don’t ask you to upload your source documents to our server for encryption.
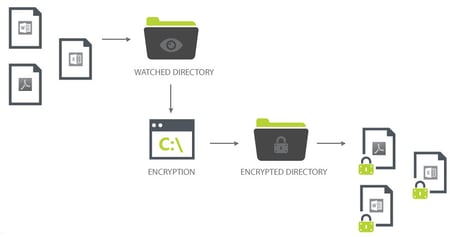
FileOpen offers several configurations for client-side encryption to meet varying business needs. At the most basic level, users simply drop their unprotected documents into a monitored directory on their machine. That action initiates the encryption process and within seconds an encrypted version of the same document is placed into a directory of the user’s preference. The file can then be distributed by any means available. If appropriate there is an option to mirror the output folder to many popular file-sync-and-share sites through oAuth or other APIs. In addition to our basic directory monitor interface, FileOpen software can be configured to programmatically encrypt all documents created on a given machine or server, as they are created or on-the-fly, as the documents are being requested.
Want to learn more? Contact us if for a quick demonstration or start a free 14-day trial.
